Energy Industry
Open Source Risk Management Practices for Software Supply Chain Security in the Energy Industry
Business Requirements
As the digitalization process in the energy industry continues to accelerate, the use of open-source components throughout the software development lifecycle is becoming increasingly prevalent. To meet internal security requirements, effectively prevent and control risks associated with open-source components, and safeguard application and software intellectual property and security in alignment with DevOps process development, a project for the procurement of software composition analysis tools has been initiated. Based on the current state of internal software development within relevant energy industry enterprises, a reasonable open-source governance plan is being formulated for the software development lifecycle. This plan aims to control the entry of insecure components at the source, comprehensively detect the integrity, security, compliance, malicious code, and version issues of third-party components during both storage and usage, and prevent problems such as application system attacks, legal risks, and intellectual property losses arising from third-party components.
Solution
Technical Architecture

Relying on the SourceSCA open-source threat management platform, we detect the composition inventory, risk components, and license agreement risks within the energy industry's internal systems. Leveraging capabilities such as source code SCA, binary SCA, and runtime SCA, we cover code/artifact repositories, delivered introduced software, and existing runtime applications to identify known risks in current inventory components or applications.
Firstly, it detects known vulnerabilities in third-party components used by applications, establishing a comprehensive vulnerability detection mechanism for timely discovery and remediation to ensure the security of application systems. Additionally, by utilizing vulnerability reachability analysis technology, it lowers the priority of vulnerabilities in declared but not yet actively used components, assisting users in making priority decisions. This approach allows limited resources to be focused and utilized more efficiently.
Secondly, it identifies security licensing issues in third-party components. By grouping licenses with similar characteristics and risks into custom license families and combining this with continuous monitoring and alerts for conflicting license clauses, it significantly simplifies the complexity users face in license compliance governance.
Lastly, it fully leverages Software Bill of Materials (SBOM) technology. By matching SBOM intelligence with their digital assets, users can perform more targeted risk warnings, threat localization, and response actions on third-party components from both vulnerability and malicious code perspectives.
Results and Benefits
By introducing the SCA platform, it assists users in the energy industry in clarifying their software component asset management ledger, thereby enabling precise target management. The platform conducts comprehensive and detailed correlation and aggregation analysis of open-source components, potential vulnerabilities, and associated license risks within applications. Whether at the source introduction stage, during the development process, in operational monitoring, or even at the management level, the platform allows for the rapid and accurate pinpointing of vulnerabilities and timely implementation of remediation measures. This multi-dimensional control model forms a rigorous closed-loop system, akin to a robust line of defense, comprehensively managing open-source threats and safeguarding the business development and information security of enterprises in the energy industry.

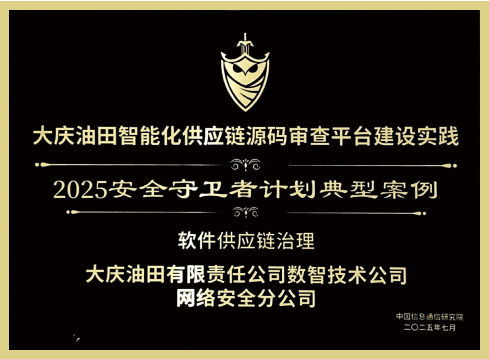
Honorary Recognition
The "Practice of Building an Intelligent Supply Chain Source Code Review Platform at Daqing Oilfield" was selected as a typical case in the China Academy of Information and Communications Technology's 2025 Security Guardian Program.
To promote the deep integration of cybersecurity technology with informatization development across various industries and fields, the China Academy of Information and Communications Technology has successfully carried out the "Security Guardian Program" typical case collection initiative for four consecutive years since 2021. Leveraging extensive practical implementation experience, the "Practice of Building an Intelligent Supply Chain Source Code Review Platform," jointly submitted by Xuanjing Security and Daqing Oilfield, was recognized as a typical case in the China Academy of Information and Communications Technology's 2025 Security Guardian Program.

Scan the QR code for access to the detailed scheme of the award - winning case.