Government and Enterprise Sector
Integrated R&D and Operations Security Solution for the Full Lifecycle of Software Application Services in the Government and Enterprise Sector
Business Requirements
A monitoring center under the China Earthquake Administration (CEA) undertakes the informatization support for national seismic monitoring data quality control, seismic disaster risk prevention and mitigation, and public earthquake preparedness and disaster reduction services. It is also responsible for key tasks such as the construction and operation of pilot platforms for seismic prediction, early warning, and forecasting technology software, the development and maintenance of industry cloud platforms, and technical support for the center's official website.With the adoption of new technical architectures including big data and cloud computing, the center faces challenges such as high-frequency application upgrades and iterations, complex development models, wide coverage, and strict timeliness requirements. A critical pain point to be addressed urgently is how to seamlessly integrate security into the existing R&D and operations system, ensuring that sensitive seismic data assets and business application systems are protected from threats.Based on its existing personnel management system and institutional processes, the center has introduced Xmirror Security's agile security toolchain (including SCA, IAST, SAST, RASP, etc.), which seamlessly integrates with the current R&D and operations platform. This implementation has solidified security capabilities such as source code security management, open source risk governance, sensitive data leakage prevention, and runtime application self-protection, effectively establishing an integrated R&D and operations security governance system covering the full lifecycle of software application services.
Solution
Technical Architecture

We comprehensively leverage tools such as SAST and IAST to conduct multi-dimensional business security testing prior to application deployment. This testing in-depth uncovers potential security vulnerabilities and business logic flaws, including but not limited to OWASP TOP 10, horizontal privilege escalation, vertical privilege escalation, batch registration, captcha bypass, and SMS bombing, while providing detailed vulnerability reproduction steps and comprehensive remediation guidelines.Simultaneously, we implement regular monitoring of runtime applications. Finally, all test results are uniformly pushed to a vulnerability management platform, where cross-team workflows are established to track the status of vulnerability handling, achieving one-stop automated closed-loop management of vulnerability risks.
Achievements and Benefits
Through open-source component risk governance, we have realized the full-lifecycle tracking of third-party dependencies, enabling early identification and remediation of high-risk vulnerabilities. This has reduced the risk of system abnormalities caused by component vulnerabilities by over 80%, fundamentally eliminating disruptions to core businesses such as seismic monitoring and early warning, as well as analysis and forecasting, resulting from security vulnerabilities and compatibility issues.The vulnerability full-lifecycle management mechanism covers the entire "development-testing-operation" phase. Combined with multi-dimensional detection using tools such as SAST and IAST, the efficiency of vulnerability discovery has been improved by 60%, with a significant enhancement in the ability to detect OWASP TOP 10 vulnerabilities and business logic vulnerabilities in particular. Supported by an automated closed-loop management process, the average vulnerability remediation cycle has been shortened by 50%, effectively preventing security incidents caused by unaddressed vulnerabilities and ensuring the continuous and stable operation of critical applications such as early warning information release terminals and seismic consultation systems.The construction of source code security control, through automated detection and version management standardization, has shifted the code defect identification node forward to the development phase. This has improved the efficiency of developers in remediating code defects by 40%. Especially for frequently iterated code such as that in seismic analysis, forecasting, and consultation systems, it has reduced rework costs caused by defect discovery during the integration and joint debugging phase, supporting the rapid iteration needs of business systems.The seamless integration of security toolchains with existing R&D and operation systems has eliminated the problem of "disconnection between security detection and business development." It enables the endogenous embedding of security capabilities without imposing additional process burdens on development teams.

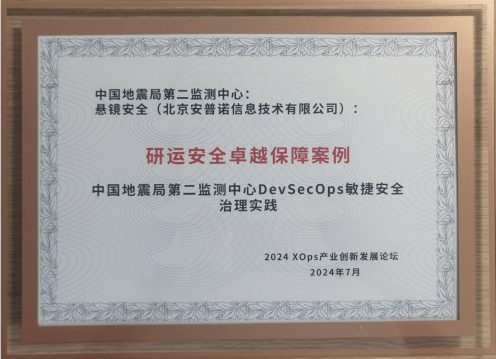
Honorary Recognition
The DevSecOps Governance Practice of the Second Monitoring Center of China Earthquake Administration was selected as an Outstanding Case in the 2024 XOps "Innovation Leadership" Awards by the China Academy of Information and Communications Technology (CAICT).
Hosted by CAICT, the 2024 XOps Industrial Innovation and Development Forum was held in Beijing with the theme "Precise Intelligence, Strategic Vision". As part of the forum, the 2024 XOps "Innovation Leadership" Outstanding Case Collection Campaign was launched. In collaboration with the Second Monitoring Center of China Earthquake Administration, Xmirror Security's DevSecOps Agile Security Governance Practice stood out among numerous submissions and was successfully honored with the "DevSecOps Excellence in R&D & Operations Security Assurance Case" award.

Scan the QR code for access to the detailed scheme of the award - winning case.